
Cybersecurity

Online Driver Update Tools for Business Cybersecurity Introduction In today’s digital age, cybersecurity is a top priority for businesses of all sizes. Protecting sensitive data…

Is AmourFeel Safe? A Full Security Breakdown
Is AmourFeel Safe? A Full Security Breakdown Finding a dating partner online can be tricky if you constantly worry about security. You have to be…

In-Depth Review of LoveFort’s Privacy & Security
LoveFort Privacy & Security: What You Need to Know Before Joining In modern times, everyone wants to be protected on the Internet, especially when looking…

Cybersecurity s for High-Net-Worth Individuals
The Intricacies of Cybersecurity for the Affluent: A Nuanced Exploration In today’s virtual time, safeguarding one’s virtual persona is paramount, especially if one’s financial footprint…

The Rise of McAfee Scams: What You Need to Know
The Tech Defense Dance: McAfee Scams and How to Sidestep Them In today’s tech-driven world, where virtual threats can feel as real as a cat…

How Cyber Security Consultancy Supports Digital Transformation Strategies
How Cyber Security Consultancy Supports Digital New Age Revamp Strategies Digital transformation has become a cornerstone for businesses looking to stay competitive in today’s fast-paced,…

Blockchain for Business: Enhancing Security & Efficiency
Blockchain for Business: Improving Security & Efficiency in the Modern Time Ah, blockchain—it’s not merely a buzzword thrown around by tech enthusiasts at Silicon Valley…

CySA+ vs Security+: Which Certification Works Best for You?
CySA+ vs Security+: Which Cert Works Best for You? In a continually developing online protection industry, certificates are critical to approving your mastery and hanging out…

How Video Production Teams Can Protect Creative Work
How Video Production Teams Can Protect Their Creative Process from Digital Security Threats The virtual time has fundamentally transformed the video production industry, making it…

From Fake Products to Payment Scams: The Importance of Cybersecurity in Building Trust with Customers
E-commerce is the way of the , available in the present. It is everywhere we go, dominating the retail trade market in a big way.…

Security Measures To Look for When Selling Concert Tickets Online
Security Measures To Look for When Selling Concert Tickets Online Online ticket resale services make it easy for sellers to reach more potential buyers. There…

Quantum Safe Or Quantum Sorry Racing To Post Quantum Security
Quantum Safe or Quantum Sorry: Racing to Post-Quantum Security Quantum computers aren’t science-fiction foils anymore; they’re ticking erasers aimed at today’s encryption. Analysts estimate attackers…

Amazon employee data stolen through MOVEit breach
Amazon Faces Data Breach: What We Know So Far In the bustling world of tech giants, security breaches are as unwelcome as a New…

Cyber Fraud in India and what Equal Plans to Do
Equal’s Strategic Initiative to Combat Cyber Fraud in India In a virtual time where data breaches and identity thefts are as common as monsoons in…

How Online Fax Services Are Changing the Game for Businesses
In today’s rapidly evolving digital landscape, businesses are constantly on the lookout for tools to enhance efficiency and streamline their operations. One such development that…

Cybersecurity for Businesses: Protecting Your Data & Assets
“` Cybersecurity for Businesses: Protecting Your Data & Assets How about if one day you are: a frantic call from your IT department at 2…

How Effective is encryption with password protection in Adobe PDFs?
Encryption and password protection play a vital role in securing sensitive information in tech documents. In this blog post, we will explore the effectiveness of…
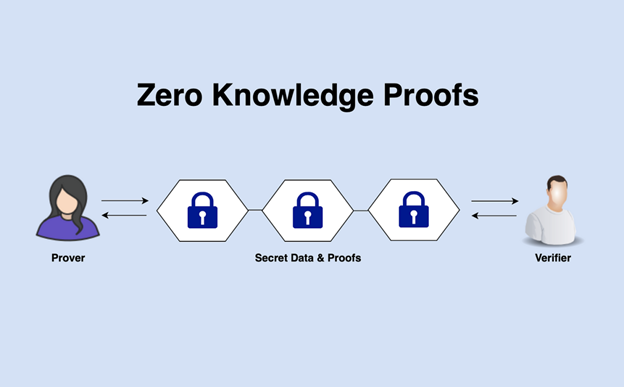
How Zero-Knowledge Proofs Are Authentication Systems
How Zero-Knowledge Proofs Are Transforming Authentication Systems Disclosure: Some links, mentions, or brand features in this article may reflect a paid collaboration, affiliate partnership, or…

How High-Quality Video Footage Improves Security Monitoring
How High-Quality Video Footage Improves Security Monitoring Security monitoring has hence evolved as a way in the provision of security both in premises belonging…

Building Trust and Credibility: The Role of Networking and Security in Marketing
Building Trust and Credibility: Networking and Security in Marketing As tech marketing and online transactions continue to grow, providing a safe and get environment for…