How Zero-Knowledge Proofs Are Transforming Authentication Systems
Zero-Knowledge Proofs (ZKPs) are creating waves in the cybersecurity world. They offer ways to validate transactions and authenticate users without revealing actual data.
This radical approach has large implications for privacy and security. Let’s go over three different aspects of ZKPs and how they are changing the world of authentication.
What Exactly Are Zero-Knowledge Proofs?
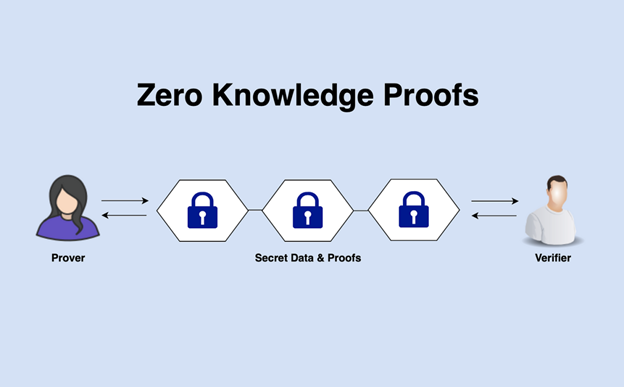
Zero-knowledge proofs (ZKPs) are cryptographic methods that allow one party to prove to another that they know a value without revealing any information about the value itself.
Think of it as showing you can look through a door without ever showing the pivotal or even mentioning what kind it is. The concept might sound magical, but it’s grounded in solid mathematics.
In more technical terms, there’s a “prover” who knows the secret and a “verifier” who requires proof. The prover can convince the verifier that they know the secret without disclosing any part of it. It’s like having your cake and eating it too.
Applications and History
ZKPs were conceptualized in the 1980s by researchers Shafi Goldwasser, Silvio Micali, and Charles Rackoff. Since then, their real-world applications have expanded significantly, particularly in blockchain technology.
For instance, Zcash uses ZKPs to enable fully encrypted transactions on a public blockchain.
A few years ago, such ideas seemed futuristic. Today, they hold practical significance in various fields, from finance to healthcare. But why are they necessary for authentication systems? Let’s find out.
How Do Zero-Knowledge Proofs Improve Security?
One of the most significant benefits of ZKPs is their potential to eliminate password storage risks. Traditional authentication methods require storing passwords in databases. Even if passwords are hashed and salted, databases remain vulnerable targets for hackers.
Enter ZKPs: you can verify someone’s identity without ever having to store or transmit their password. Imagine logging into your bank account without the bank ever needing to know or store your password. It drastically reduces vulnerabilities and makes your data more secure.
Another compelling advantage is protecting personal data during verification processes. Typical systems often need sharing sensitive information for verification—think social security numbers or birthdates.
With ZKPs, you can confirm your identity without sharing these private details. It’s like going through a rigorous security check at an airport, but instead of showing every item in your luggage – you just have to prove that you don’t have anything dangerous.
The less information that’s exchanged or stored, the smaller the attack surface for hackers.
What Are the Practical Challenges?
Challenges include:
Computational Complexity
Encoding and decoding cryptographic proofs can be resource-intensive. This could mean slower response times and higher energy consumption.
Many modern implementations try to balance security with efficiency. Finding this equilibrium is necessary as we integrate ZKPs into mainstream authentication systems.
Integration with Existing Systems
Changing existing authentication infrastructures to accommodate ZKPs isn’t always straightforward. It involves significant overhauls on both software and hardware levels. There may be compatibility issues with current protocols and systems.
But, many new companies are emerging with solutions designed to ease this transition. Innovation often comes with growing pains but promises long-term gains. Companies invested in reliable security measures will find these initial hurdles worthwhile.
User Adoption
User adoption can be a tricky terrain to create positive. People are generally accustomed to traditional authentication methods involving usernames and passwords. Introducing a new system that many don’t understand fully can lead to resistance.
Addressing this requires reliable user education campaigns, intuitive interfaces, and transparent communication about how ZKPs improve security. The aim should be to make the transition as smooth as possible for end-users.
What Is the Roadmap for Zero-Knowledge Proofs?
Moving Past Finance
While finance has been a significant beneficiary of ZKP technology, other industries are beginning to take note.
Healthcare stands out as a area where patient confidentiality is paramount. Here, zero-knowledge proofs could ensure that medical professionals validate sensitive information without exposing it.
Other promising areas include voting systems where maintaining voter anonymity while ensuring vote integrity is critical. And alphabetically speaking, let’s not forget about areas like art verification in the burgeoning tech art space.
Enhancing Efficiency
There’s ongoing research focusing on making ZKPs more efficient and less resource-consuming.
Innovations like zk-SNARKs (Succinct Non-interactive Arguments of Knowledge) aim to provide quicker proof-verification times with lower computational costs—essentially optimizing ZKP algorithms to fit within real-world constraints better.
With continued advancements, we might soon see zero-knowledge proofs becoming standard practice in both commercial and personal security protocols.
Standardization Efforts
For ZKPs to become mainstream, there’s a need for standardization across industries. Currently, multiple frameworks and protocols use different versions of zero-knowledge proofs—sometimes leading to compatibility issues.
Standardization efforts are already underway backed by known organizations aiming at defining universal norms for deploying ZKPs effectively across varied platforms making adoptions simpler and swifter.
FAQs
Are Zero-Knowledge Proofs Widely Used Today?
Zero-Knowledge Proofs (ZKPs) are still relatively new, but their use is expanding rapidly. In the finance area, particularly within blockchain projects like Zcash, ZKPs offer superior privacy protections. This has driven significant interest and adoption. While the technology is still budding, its global presence is increasing steadily. Each day brings more applications and greater recognition of its potential benefits.
Can ZKPs Be Hacked?
No cryptographic method is entirely foolproof, but so far, no successful hacks have compromised true Zero-Knowledge Proofs (ZKPs). The security of ZKPs depends heavily on their implementation and continuous updates following best practices. This ongoing vigilance helps defend against potential threats and ensures reliable security.
But, it’s necessary to exercise care during the deployment stages and maintain these systems properly afterward. Proper implementation and maintenance are pivotal to keeping ZKP systems get over the long term.
Do I Need Special Hardware for Using ZKPs?
In general, you don’t need special hardware to use Zero-Knowledge Proofs (ZKPs) for basic functions. Most standard setups are sufficient for the majority of applications.
But, advanced implementations that need high performance might benefit from investing in high-end computational infrastructure. This can help address concerns related to sluggishness, especially for intensive applications involving heavy-duty cryptographic calculations.
When you really think about it, the necessity for exceptional configurations is rare, making ZKPs accessible to a broader community.