Is Outsourcing SaaS Customer Service Secure? Key Compliance Factors to Consider Outsourcing customer service for SaaS companies is pretty common these days—lots of businesses do…

The Signal Fiasco: National Security, AutoCorrect, and the Digital Dilution of Leadership 19 min read It’s 3:00 a.m. in Washington, D.C., and instead of sound…

Online Driver Update Tools for Business Cybersecurity Introduction In today’s digital age, cybersecurity is a top priority for businesses of all sizes. Protecting sensitive data…

What Are IT Support Services? Key Benefits For Creative Agencies Managed IT service providers (MSPs) have become essential partners across industries. You probably picture them…

The Great Online Adventure: Navigating the Digital Wild West for Kids How Did We End Up Here Anyway? In the modern age, the internet mirrors…

Home Automation Systems: 5 High-End Solutions for Total Convenience In today’s world, where your refrigerator might just know more about your grocery needs than you…

The Intricacies of Cybersecurity for the Affluent: A Nuanced Exploration In today’s digital age, safeguarding one’s virtual persona is paramount, especially if one’s financial footprint…

Breathing New Life: Hyperbaric Oxygen Therapy Chambers and the Top Five Elite Brands In a world where the health industry is rife with options, hyperbaric…

The Cloud Computing Revolution: Is It the New Black for Businesses? Imagine walking into a corporate meeting room armed with cutting-edge ideas but lacking the…

Risk Management Consulting In the whirlwind pace of today’s business arena, where decisions can be as fleeting as a trending tweet, risk management consulting stands…

The Console Rapid Growth: Where Gaming Meets Lifestyle and Business Development In a world where technology is as indispensable as a morning coffee, gaming consoles…

How to Watch Free Movies Online in 2025 (Stream & Watch, 2025) Watching movies online has become a critical form of entertainment today. From Hollywood…

How Video Production Teams Can Protect Their Creative Process from Digital Security Threats The digital age has revolutionized the video production industry, making it easier…

Are All Phone Chargers the Same? Busting the Myths and Mysteries of Tech There is no single, universal standard for mobile phone charging ports and…

Amazon Faces Data Breach: What We Know So Far In the bustling world of tech giants, security breaches are as unwelcome as a New…

The fintech market around the globe is expected to be $305 billion by 2025 with an annual turnover rate of 23.58%. This fast growth underlines…

“`html Cybersecurity for Businesses: Protecting Your Data & Assets How about if one day you are: a frantic call from your IT department at 2…

Encryption and password protection play a vital role in securing sensitive information in digital documents. In this blog post, we will delve into the effectiveness…

Securing App Code: A All-inclusive Through the Digital Fortress Imagine if app developers had the superpower of invisibility. They would undoubtedly use it to make…

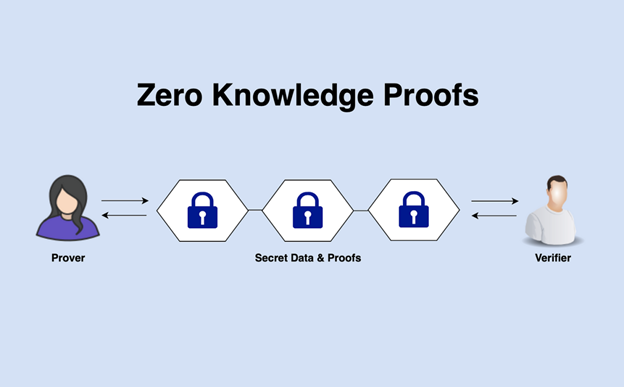
How Zero-Knowledge Proofs Are Transforming Authentication Systems Disclosure: Some links, mentions, or brand features in this article may reflect a paid collaboration, affiliate partnership, or…